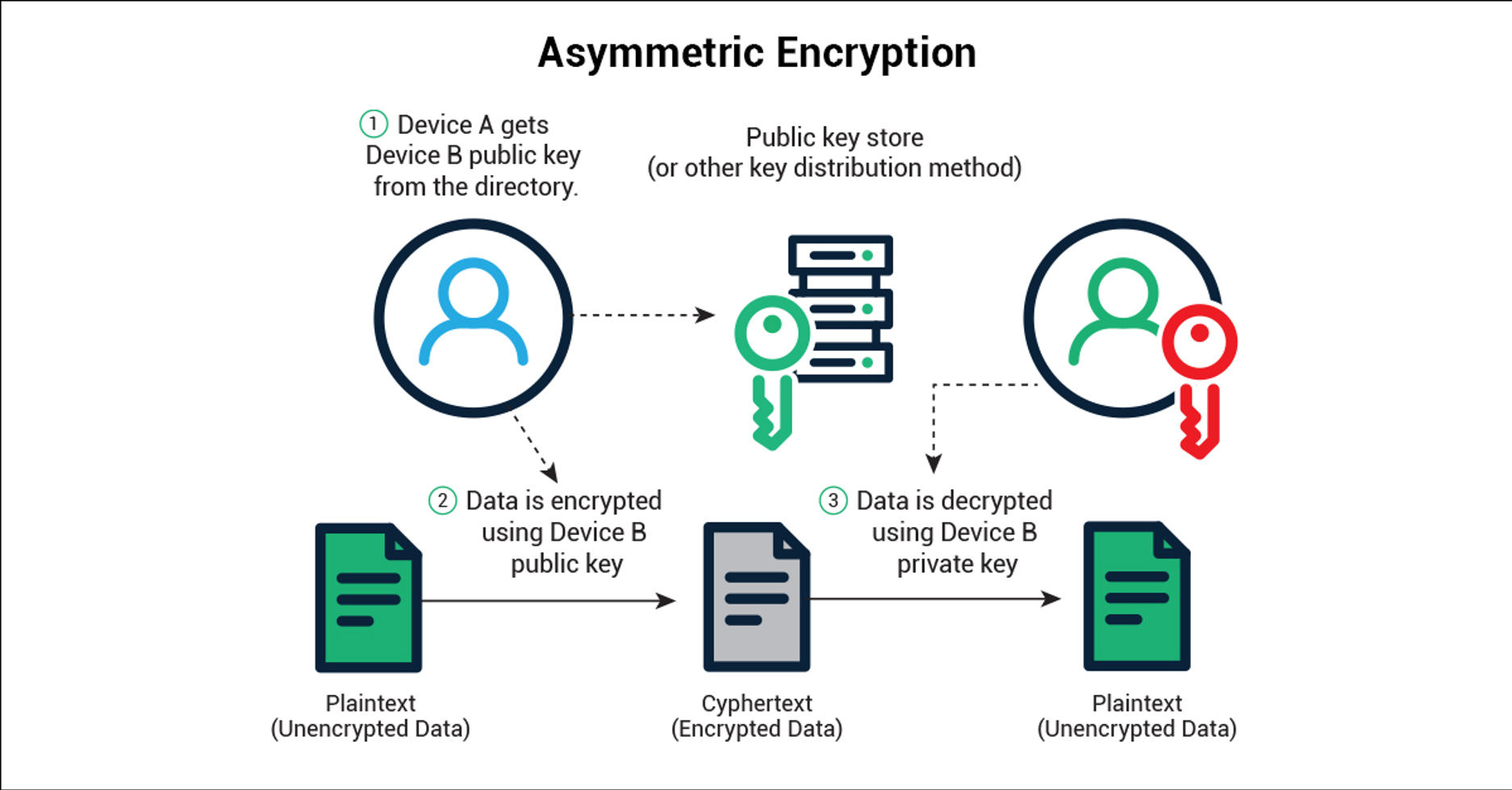
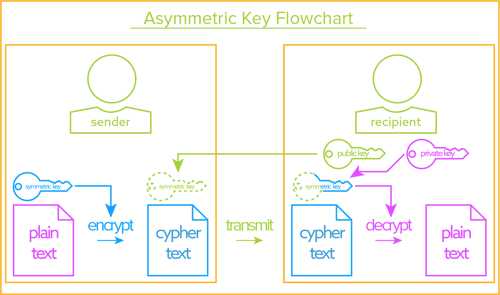
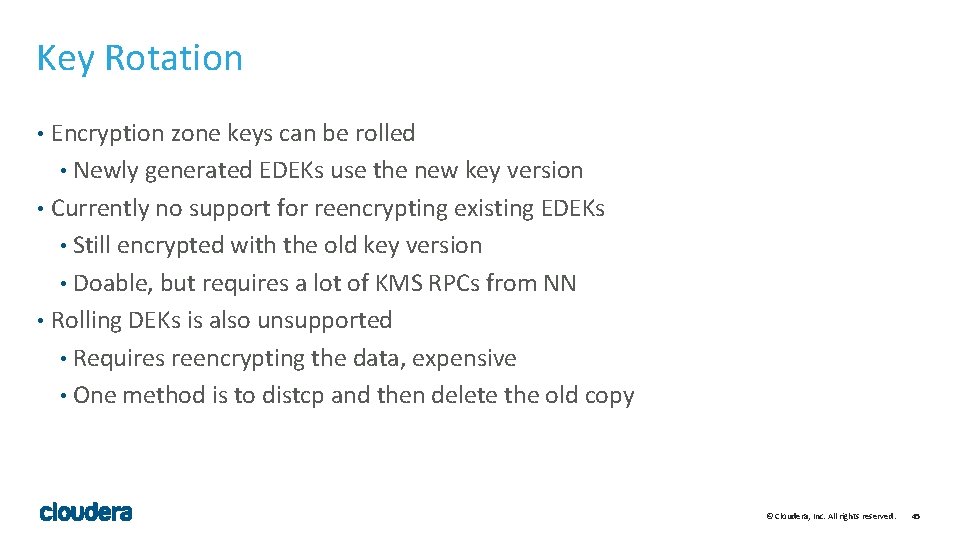
Smart access control elevator card encryption ICID copy machine Rolling code copykey copy Qi X5 universal key cutting machine

433mhz Garage Door Remote Control Universal Car Gate Cloning Rolling Code Remote Duplicator Opener - buy from 5$ on Joom e-commerce platform

Smart access control elevator card encryption ICID copy machine Rolling code copykey copy Qi X5 universal key cutting machine